As we get closer to 2025, antivirus software will play a bigger role in protecting computers and devices from malware, viruses, and other online threats than it ever has before. That’s because with every passing year, threats increase and the value of our personal data becomes even greater. The good news is that many of the top antivirus companies offer free versions of their products with solid core protection. These free options can provide robust security for budget-conscious users or those wanting to try before buying a paid version. Having reliable antivirus protection is more critical than ever and the free antivirus programs listed here offer robust protection against a wide array of online threats, from viruses and Trojans to ransomware and spyware.
When choosing a free antivirus, it’s important to look at features like real-time scanning, malware detection rates, and impact on system performance. Some popular free antivirus options include Avast One Basic, Avira Free Antivirus, Bitdefender Antivirus Free, and Microsoft Defender. Each has strengths in areas like ease of use, extra features, or lightweight system footprint.
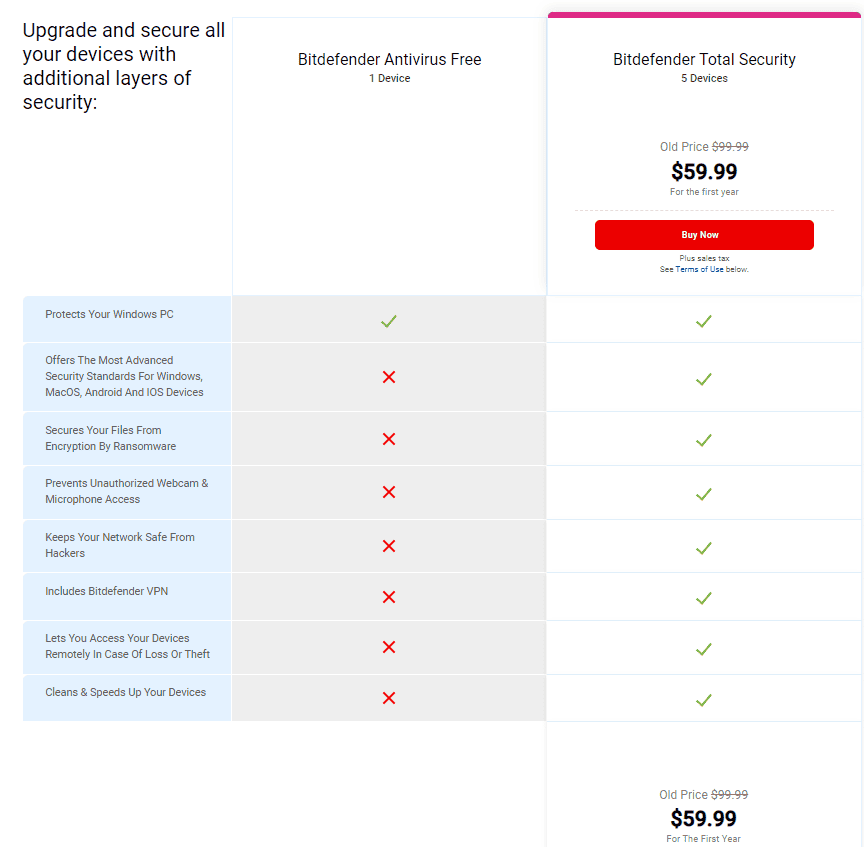
Free antivirus software can offer good basic protection, but paid versions often include more features. Things like VPNs, password managers, and advanced firewall protection are usually limited to premium tiers. Still, a quality free antivirus is much better than no protection at all for keeping devices safe from common threats.
Staying Safe Online: Top Free Antivirus Picks for 2025
Keeping your computer safe from viruses and malware is essential, but you don’t always need to pay for top-notch protection. Many excellent free antivirus programs offer robust security without costing a dime. Here are a few of the best options to consider in 2025.
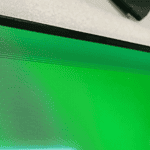
1. Bitdefender Antivirus Free Edition
Bitdefender is the hands down winner for Free Antivirus protection in 2025 and you’ll be happy to know that the full suite of tools they provide is nearly unmatched. Bitdefender has always been known for its powerful antivirus engine, and its free edition provides a streamlined, easy-to-use experience that is both powerful and easy on your system resources. It’s perfect for users who want reliable protection without a lot of bells and whistles.
Pros:
- Excellent malware detection rates
- Simple and user-friendly interface
- Minimal impact on system performance
Cons:
- Limited features compared to the paid version
- No customization options
2. Malwarebytes Free
Malwarebytes Free is a fantastic on-demand scanner that excels at catching and removing stubborn malware. It’s a great tool to use in conjunction with another antivirus program or Windows Defender.
Pros:
- Powerful malware removal capabilities
- Catches threats that other programs might miss
- Ideal for occasional scans and second opinions
Cons:
- Free version doesn’t offer real-time protection
- Requires manual scans
3. Sophos Home Free
Sophos Home Free offers a surprising number of features for a free antivirus program. It includes real-time protection, ransomware protection, web filtering, and even parental controls.
Pros:
- Good malware detection rates
- Includes extra features like web filtering and parental controls
- Easy to use
Cons:
- Can be a bit more resource-intensive than some other options
- Limited customization
4. Avira Free Security
Avira Free Security combines a solid antivirus engine with a free VPN, making it a great choice for users who prioritize online privacy and security.
Pros:
- Good malware protection
- Includes a free VPN with limited data
- User-friendly interface
Cons:
- Can be a bit more resource-intensive than some other options
- Free VPN has data limits
5. AVG AntiVirus Free
AVG AntiVirus Free is a long-standing and well-respected name in the antivirus world. It offers reliable protection and a straightforward interface.
Pros:
- Decent malware detection rates
- Simple and easy to use
- Lightweight
Cons:
- Limited features compared to the paid version
- Can sometimes be a bit aggressive with pop-ups
Choosing the Right Antivirus for You
The best free antivirus for you will depend on your individual needs and preferences. Consider factors like the level of protection you need, the features that are important to you, and the impact on your computer’s performance.
| Rank | Antivirus | Best For |
|---|---|---|
| 1 | Bitdefender Antivirus Free Edition | Users who want simple, reliable protection without extra features |
| 2 | Malwarebytes Free | Occasional scans and supplemental malware removal |
| 3 | Sophos Home Free | Users who want extra features like web filtering and parental controls |
| 4 | Avira Free Security | Users who want a free VPN included with their antivirus |
| 5 | AVG AntiVirus Free | Users who want a well-known and reliable antivirus with a simple interface |
Bitdefender Antivirus Free Features:
Key Takeaways
- Free antivirus software provides basic protection against common online threats
- Top free options include Avast, Avira, Bitdefender, and Microsoft Defender
- Paid versions offer more features but free antivirus is better than no protection
Evaluating Free Antivirus Software
Choosing the right free antivirus software requires careful evaluation. Key factors include features, performance, and usability. These aspects help users find the best protection for their needs.
Feature Comparison
Free antivirus programs offer different levels of protection. Most include basic malware scanning and real-time protection. Some add extras like ransomware shields or phishing protection.
Bitdefender Free provides core antivirus features from its paid version. Avira Free offers a software updater on Windows. AVG AntiVirus Free includes suspicious activity alerts.
Users should check if the free version has a firewall or VPN. Gaming modes can be useful for players. Browser extensions often come with free antivirus to guard web browsing.
Performance and System Impact
Antivirus software can affect computer speed. Light programs run quietly in the background. Heavy ones may slow down the system during scans or updates.
Independent labs like AV-Test and AV-Comparatives test antivirus impact. They measure factors like scan times and system slowdown. Users should check these results when picking software.
Some free antiviruses perform well in tests. Others might trade speed for stronger protection. It’s important to find a balance that works for each user’s needs and hardware.
Ease of Use and Interface
A good antivirus should be simple to use. Clear layouts help users find features quickly. Easy settings let people adjust protection levels.
Some free antiviruses have basic interfaces. Others offer more detailed controls. Look for programs with clear scan results and easy-to-understand alerts.
Setup should be straightforward. Updates should happen automatically. The best free antiviruses don’t need much user input to work well. This helps keep computers safe without constant attention.
Windows Security (Formerly Windows Defender)
Before you jump into third-party antivirus options, it’s important to acknowledge the built-in security that comes with Windows. Windows Security / Defender has significantly improved in recent years, offering real-time protection, automatic updates, and decent malware detection rates. For many users, especially those who practice safe browsing habits, Windows Security may be sufficient for basic protection.
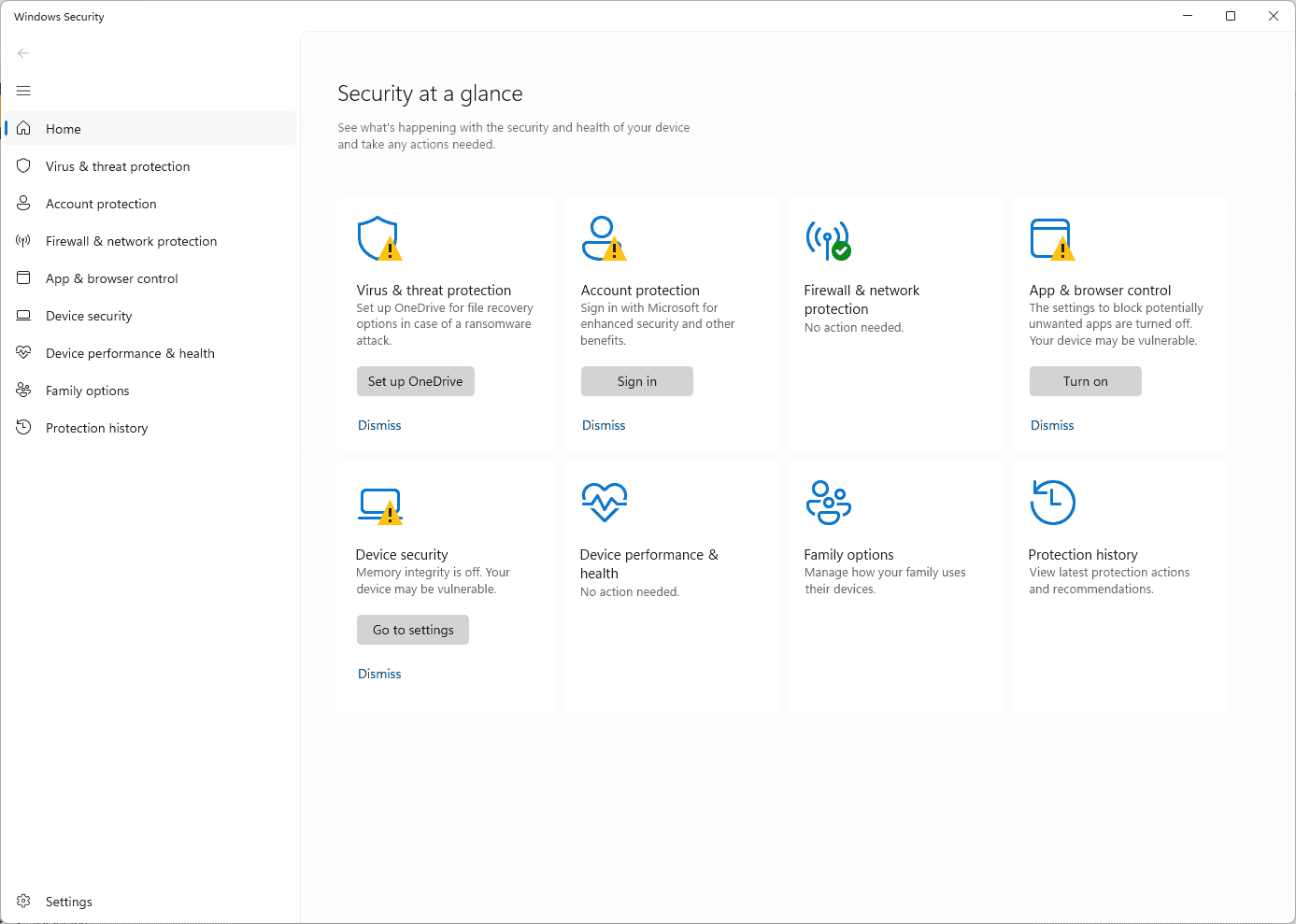
However, it’s often beneficial to add another layer of security with a dedicated antivirus program, particularly if you engage in activities that might increase your risk of encountering malware (like downloading files from untrusted sources or frequenting potentially risky websites).
A Note on Kaspersky and the U.S. Ban

Kaspersky is a well-known antivirus company with a strong track record in malware detection. However, it’s important to be aware that the U.S. government has banned the use of Kaspersky products in federal agencies due to concerns about potential ties to the Russian government. While Kaspersky remains available for home users, this ban has raised some concerns about data privacy and security. If you’re considering Kaspersky, it’s crucial to weigh these concerns against its strong antivirus capabilities and decide if it’s the right choice for you. Many excellent alternatives are available if you prefer to avoid any potential risks associated with the ban.
FAQs
Is There a 100% Free Antivirus?
Yes, there are several excellent antivirus programs that offer 100% free versions with no hidden costs or required subscriptions. These free versions typically provide core antivirus protection to safeguard your computer from common threats. Some popular options include Bitdefender Antivirus Free Edition, Malwarebytes Free, Sophos Home Free, Avira Free Security, and AVG AntiVirus Free.
Is Avast Antivirus 100% Free?
Avast used to offer a fully free antivirus, but they have shifted their focus to paid products. While they still have a free version, it’s more limited in features compared to their paid options. If you’re looking for a completely free antivirus with strong protection, Bitdefender or Malwarebytes might be better alternatives.
Can Free Antivirus Be Trusted?
Yes, many free antivirus programs from reputable companies can be trusted. They offer reliable protection against common viruses and malware. However, it’s important to choose a well-known and trusted brand. Always download antivirus software from the official website to avoid fake or malicious versions.
Is Malwarebytes 100% Free?
Malwarebytes offers both free and paid versions. The free version is a powerful on-demand scanner that you run manually to check for and remove malware. It’s great for occasional scans and as a second opinion. However, it doesn’t offer real-time protection like the paid version.
Which is Better: McAfee or Malwarebytes?
Both McAfee and Malwarebytes are reputable security companies, but they have different strengths. McAfee offers a more comprehensive suite of features, including real-time protection, a firewall, and anti-phishing tools. Malwarebytes excels at removing tough malware and is known for its powerful on-demand scanner. The best choice for you depends on your specific needs and preferences.
Why Not Use Malwarebytes?
While Malwarebytes is a great tool, the free version has some limitations. It doesn’t offer real-time protection, so it won’t actively prevent malware infections. It also requires manual scans. If you’re looking for always-on protection, you’ll need to consider the paid version or a different antivirus program.
Is Malwarebytes Still the Best Free Antivirus?
Malwarebytes is a top contender, especially for its malware removal capabilities. However, other excellent free antivirus programs are available, such as Bitdefender Antivirus Free Edition and Sophos Home Free. These offer real-time protection and other features that Malwarebytes Free doesn’t include. The “best” choice depends on your individual needs.
Should I Get Norton or Malwarebytes?
Both Norton and Malwarebytes are well-regarded security products. Norton offers a more comprehensive suite of features, including real-time protection, a firewall, and parental controls. Malwarebytes is known for its powerful malware removal and on-demand scanning. Consider your needs and budget when choosing between the two.